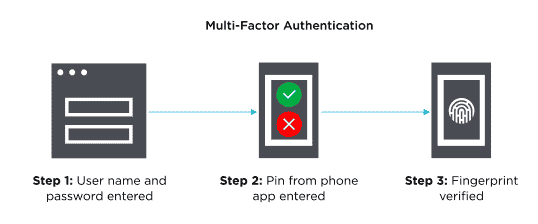
Learn to Implement Multi-Factor Login Authentication
Why passwords alone aren’t enough
Let’s be honest: most of us recycle passwords. One for Gmail, another for Instagram, maybe a simple one for some old forum. And hackers? They know this. Password leaks happen constantly. That’s why multi-factor authentication, or MFA, is a game-changer.